Are you looking for the difference between VPN and RDP? If yes, then this article is for you. In this article, we have comprehensively covered everything you need to know about VPN and RDP.
A secure connection is a topmost priority in the digital world for professionals who need to work remotely on confidential data. While several means exist to create a safe link with the data servers, VPN and RDP are the most sought-after options.
But even after their widespread usage, people still confuse these technologies to be the same, which is far from reality. These connections have extremely different features and applications. The target consumers for each are different. And so are their privacy vulnerabilities.
With the increase in remote culture for education, work, business, and other online activities, there is much need to understand which tool to use to create secure connections with the servers. Not only will this understanding help you to choose the perfect tool but also to save time and resources spent on unnecessary software.
This article will discuss VPN and RDP and learn about their mode of operation, pros and cons, unique features, and what distinguishes them from each other. The article will help you decide which option to select that fits your requirement.
Virtual Private Network (VPN)

In simple words, a Virtual Private Network acts as a tool that allows the user to create a private network in the public Internet by creating an encrypted tunnel over the existing connection. So even when the connection is through open networks, a bypass with an encrypted and safe channel to transfer data between the user and the server is possible.
The importance of such a connection is evident when a user needs to access classified proprietary files and applications in a server while connected to public network connections. Several security threats appear while browsing through such connections, whose mitigation is possible through a VPN.
An added benefit of a VPN is that while creating a private network over the existing network, it transforms the user’s location into a random location preventing tracking by others in the same public network.
The general population might only use VPN to create a fake profile of location, which prevents sharing the user’s actual location. But professionals utilize a VPN for various applications to enable protected files, data, and communication. Let us take a look at the types of VPN and their features.
Types of VPN:
Categorization of VPN is by its modus operandi or configuration of network used. Organizations extensively use VPN with many offices and remote workers who need to connect to a server usually situated at a headquarter. Such VPNs have classifications based on the network connectivity protocols. Given below, in brief, are some general classifications.
1. Host-To-Betwork Remote Access VPN:
Individuals use host-to-network remote access, the most basic VPN, to access the local area network while being anonymous. Such VPN is usually preferred by people who require the anonymity feature provided by VPNs. Most computer and mobile operating systems support remote access through proxy networks, whose configuration is in very few steps. It scarcely costs any money and can provide adequate security for a VPN.
2. Intranet Site-To-Site VPN:
The application of intranet site-to-site VPN is to connect two servers or networks to transfer information. The use of such VPN is by establishments with two branches and need the data storage to be at any single location to avoid any cyber-attacks or hacking. The setup of such VPN may be costly as exclusive software is a need for transfer.
3. Extranet Site-To-Site VPN:
Extranet site-to-site VPN also has the same features as intranet site-to-site and may be pricey. Still, it has added features to facilitate multiple sites, server interconnections, and remote access. The use f such VPN is by large industries and multinational companies to have secure networks where multiple branches can log in to a single server. Remote workers of the company can also access this network from anywhere.
4. Client-Oriented VPN:
Client-oriented VPN requires a mediator application to access the Internet through safe tunneling modes. Use of such applications is for casual purposes where the IP spoofing of the user is possible, or the access is only restricted to users in a specific geographic location. Most available VPN software is freely accessible and seldom requires paid versions to intensify security features.
5. Network Oriented VPN:
Network-oriented VPNs connect private networks through a public network with enhanced data safety features. For such VPNs, the mode of WAN tunneling is through IPsec Tunnels, MPLS-based L3VPN, and Dynamic Multipoint VPN.
Advantages of Using a VPN
1. Secure Network: VPN can provide the user with a secure network where data leaks during transfer are not possible.
2. Secure Private Information: The private information and the user’s identity aren’t breached while accessing public networks by other users connected to the same network.
3. Data Throttling Prevention: Some VPNs benefit the users by bypassing the internet provider’s data capacity usage. This benefit is because some providers cannot see the data used, and thus the data consumed in their record will be lower than the actual data consumed.
4. Bandwidth Throttling Prevention: There are also internet providers who lessen the bandwidth or internet speed after a certain amount of data consumption. A bypass in this throttling with the help of a VPN is possible.
5. Access to Geo-Blocked Services: A VPN can create a virtual IP in faraway places giving the user access to geographically blocked internet services in their location.
6. Network Scalability: The use of VPN is also by companies that look forward to expanding their network of professionals working on paid software and techs. Thus, even if one or two systems in an organization have some particular software, everyone can remotely access the system to use the software. Such a common system saves a lot of money for the organization and widens its expansion schemes.
7. Cheaper Support Costs: Several VPN software is available in the market for free usage. Some extra features might need payment, but the basic functions are accessible without any charge.
8. Firewall Bypassing: Bypassing the firewall of the system that we are using is also possible while using VPN as the network is being accessed through a virtual location and has nothing to do with the working system.
9. Affordable Security: VPN provides a secure connection at very little to no cost. This low cost is the reason for attraction for various individuals who use VPN only for entertainment and browsing purposes.
10. Protected File Transfer: Another great feature of a VPN is that the file transfer between systems is secure from hacking due to inbuilt IPv4 and IPv6 protocols.
Disadvantages of Using a VPN
1. Risks Associated with the Free Application: Even though the information shared through VPN software is not visible to the network provider and other users, it can be easily accessible by the software developer. As most VPN software development is by private companies, the motive behind the software being free is questionable.
2. Better Quality VPNs are Costly: The quality of the unpaid version of the software is questionable and might require upgrading to a paid version for all features to activate.
3. Slower Internet Speeds: The greatest drawback of VPN is the reduced internet speed. It occurs due to data transfer through tunneling, which might not support your local bandwidths, or due to data transfer through an arbitrator application.
4. Not Available on All Devices: VPN is not available on all devices. Some mobiles have proxy network connections similar to a VPN, but this is not available in older products.
5. Occasionally Difficult Configuration: Configuration of VPN is an easy task for a professional, but if there are changes in protocol listing methods, a comparatively fresh user might find it complex to configure. This trouble happens because the configuration settings vary from device to device.
6. Website’s VPN Blocker: The main job of a VPN blocker embedded in a website is to block any users from using VPNs while accessing their site. The objective behind such VPN blockers is to prevent users from violating geographically protected content.
7. Intermittent Connection Drop: While accessing a website through VPN to ensure a safe passage, the connection needs intermittent cutting short to avoid user tracking. Such regular connection drops may seem troublesome while transferring large files or streaming content.
Remote Desktop Protocol (RDP)
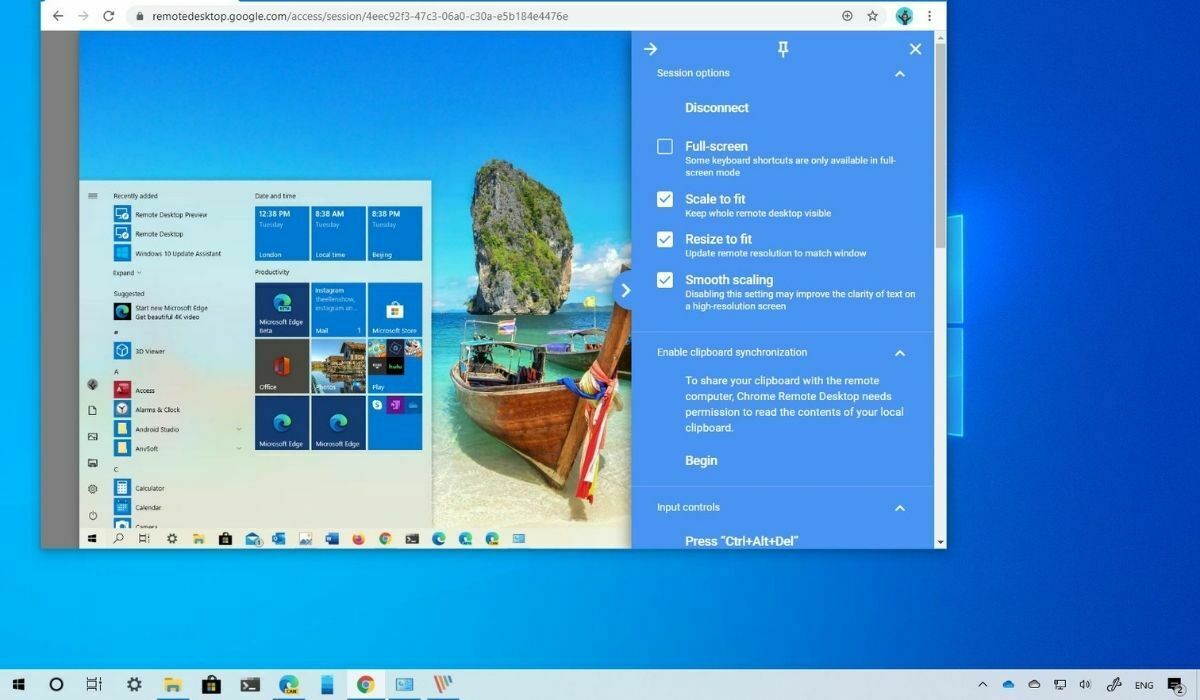
Remote Desktop Protocol, known as RDP, is a branded protocol developed by Microsoft and later adopted in other forms by various developers to remotely access a server or system from a distantly located system. In other words, an RDP allows a user to use another system located elsewhere as if they were operating it in person.
An RDP doesn’t require a complex configuration. A computer with Microsoft OS has inbuilt facilities of RDP with the name Remote Desktop Connection. Similar protocols exist in other OSs with slight changes in name, or private and free software is available in the market for remote connection.
An RDP allows the remote user to access every device attached to the host system so that a remote user can get uninterrupted access to devices like mouse, keypad, printer, web camera, microphone, installed applications, storage, and other connected appliances.
The main benefit of having such RDPs is that even when an employee cannot be present on-site, they can log into their work PC and system through any PC located in any part of the world.
Types of RDP
Classification of RDP can be in two types according to who developed it. The benefits and features of RDP change with the type of developer. The given below are the main two types of RDPs available.
1. RDP Developed by Operating System:
Following the footsteps of Microsoft, all subsequent releases had an RDP in one form or the other. Other OS developers integrated RDPs because due to the popularity of Microsoft’s RDP, many private developers were releasing applications with data hacking possibilities, and such threats started affecting the overall safety. By providing inbuilt RDP, the OS developers gave the user a first-hand experience of a safer RDP.
2. RDP Developed by a Third Party:
Private developers recreated RDP as a standalone application that can run on most devices across various OSs. Even though such RDP was initially seen as a threat to security, they later gained trust through inbuilt encryption and rapid data interchange. Some private RDP is free to use, while some generate revenue through ads or paid bonus features.
Advantages of Using a RDP
1 Secure Connection: Using an RDP ensures that the connection between two or more systems is safe from outside attacks. With limited access to users, the host can ensure extra safety in their server.
2. Work from anywhere: RDP can help allow workers to work remotely and log in to their workstations from the comfort of their homes.
3. Economical: Usually, an RDP integration is available within the OS so that the user doesn’t need to pay anything extra. Other than that, some private developers also provide high encrypted tools free of cost to users.
4. Simple configuration: The configuration of an RDP can be as simple as just inputting the user ID and password to dialing a code through an external application.
5. Quick access: As the only transfer in an RDP is input from the user to host and displayed in the host’s monitor to the user’s monitor, the data exchange is too low. With such a low amount of data consumption, RDP’s access and running speed is much higher.
6. Clipboard Sharing: An RDP inbuilt with the OS allows sharing the clipboard to copy-paste text and files to and fro the systems efficiently.
Disadvantages of Using a RDP:
1. Downtime: One of the most extreme disadvantages of RDP is that due to the high number of dependents if there is some critical flaw, it may take down the entire system and the downtime is very high when considering the cumulative number of non-working employees or users.
2. Network Dependent: A stable RDP connection requires a stable network, making RDP extremely network dependant.
3. Blockages: Sometimes, the high number of users to a particular server or a standalone application causes blockages in transfers that sabotage the entire protocol or application.
4. Reliable Network Required: An RDP also requires a trustworthy network to ensure no unauthorized access to servers or some breach that discloses data from the host.
5. Minimal Login Process: The login to the remote desktop can sometimes be too easy as just logging in with credentials. So, if these credentials get disclosed, anyone can log in to the system and access confidential data.
VPN and RDP: What’s Similar and What’s Different?
There is much confusion because of just one or two similarities between VPN and RDP. There is much confusion that both are the same and serve the same purpose. It is not true, as both have different applications and features while using different tools. The given below are some of the similarities and differences that stand out.
Similarities Between VPN and RDP
1. Data Encryption:
Data encryption and data safety are the main features of both VPN and RDP. While VPN has integrated encryption tools, RDP has data stored in encrypted form in the server.
2. Private Access:
VPN and RDP both provide a private network for the user to browse. While the private network provided by VPN allows the user to browse through the entire Internet or a server, the private network provided by RDP is just the data stored in the server.
Differences Between VPN and RDP:
1. Core Purpose:
The core purpose of a VPN is to provide safe access to a network through tunneling, whereas that of an RDP is to access a server to transfer data and information remotely.
2. Security:
A VPN doesn’t always need security integration or encryption features, as most standalone VPN applications charge extra for security features. An RDP cannot be safe as anyone with login details can easily access the server.
3. Usage:
The usage of a VPN and RDP is extremely different. While VPN is just a tool that spoofs your IP address allowing you to retrieve data already uploaded to a server, RDP allows file-sharing of all files in both servers.
4. Flexibility
A VPN can is more flexible as all the data in the server can be accessible at any time. But an RDP requires the host server to be active to grant access to the user.
5. Cost
Both VPN and RDP are available for free, and the OS is available through third-party developers’ applications. The cost of paid software is also almost similar, but the main cost-benefit is the time and resources saved using either tool.
While VPN only allows secure access, an RDP’s utilization is in an organization with remote employees and remote workstations. Such a remote work structure can benefit the organization to save many collateral costs bore solely by the organization.
Virtual Private Network and Remote Desktop Protocol: Which Tool to Choose?
Looking at the advantages and disadvantages of using Virtual Private Network and Remote Desktop Protocol, we can conclude that VPN is just a tool to bypass public networks, and RDP provides the best possible remote access with integrated security features of the server.
One should always choose an RDP when the requirement is to remotely access a server to maintain the privacy of the data transferred. While using a WAN or LAN with a host server, there are chances for some viruses to transfer from the user system to the server system.
These viruses are avoidable with the help of RDP. RDP provides limited transfer of input commands and visual illustration. Any other transfer of files is through the secure passage of the RDP, which acts as a firewall blocking the transfer of harmful files.
Frequently Asked Questions?
The comparison of RDP and VPN is impossible as both the tools have distinct features but provide the same objective to access remote servers. VPN uses tunneling over an existing network to create a private data transfer. And RDP allows access to another server through a public network remotely.
Still, while the network may be open, the host server has security features to avoid breaches, thus preventing any cyber-attacks. A VPN may not always be safe as even with integrated security features. So, considering the scenario to choose only one tool, RDP will be a better choice due to improved safety.
Yes. Applying both technologies together increases the safety in the network, and saving the server from a breach is possible.
Usually, the internet provider or anyone logged into the same network can track a user. Also, an RDP that is free or is available with the OS lacks some safety protocols. But enterprise RDPs don’t face this issue due to integrated encryption tools and firewalls. So, make sure that the RDP you use has encryption enabled or not.
There are several paid software that one can use as an alternative to RDP.
Below are some extensively used applications:
– SolarWinds Dameware Remote Support
– SolarWinds Dameware Remote Everywhere
– Royal TS
– Supremo Remote Desktop
– Zoho Assist
– Screens
– VNC Connect
– LogMeIn
– TeamViewer
– GoToMyPC
– Terminals
– Red Hat Virtualization
One of the best alternatives to RDP is SolarWinds Dameware Remote Support which is the best option for remote connection. It provides a platform to create various tech units that can be solely connected to specific workstations. This platform prevents the user from browsing or accessing any website or file that the administrator doesn’t approve. It is best for enterprises with a large number of professionals.
Yes, one can hack an RDP. From the very beginning, RDP had the negative publicity of a weak firewall without any encryption. Even with integrated encryption in the later versions of RDP, the safety issues were plenty.
As in recent years, it has come to light that the access information of some high-level RDPs is available on the dark web for sale. Such news affects the goodwill of the new RDP and makes people hesitant o choose RDP over VPN.
Final Words
Whether to choose RDP or VPN depends on the requirement of the user. Both are exclusively used for secured access, but they provide an entirely different plethora of tools. While there are some downsides to using RDP, the benefits are innumerable.
During the pandemic of COVID-19 and the boom in digitalization that followed, RDP gained much importance in the business world. Many organizations are now looking to transfer to fully remote workspaces, which is only possible through RDP and development.
We at TryRDP providers the best and most affordable RDP services. Our servers are located in different locations, including the US, UK, Canada, and are equipped with the latest hardware. Click here to check out the pricing.
We hope this article is about the difference between VPN and RDP is helpful to you. Do share this content on social media if you find it helpful for you in any manner. Please stay connected with us for such informative content.
